Apple devices are known for their security , with the help of strong authentication. Latest iOS version has improved the security of devices by stren
Read MoreA new vulnerability has just surfaced that can compromise your Linux system by pressing the Enter key. The issue is available within the Lin
Read MoreNowadays Cyber threat is a major problem in day to day life of technology where attackers always keep on digging to find the loophole. One of the maj
Read MoreRecent email scam informs you that parcel was not delivered and is awaiting pick up. You are requested to print label and pick up a parcel in the offi
Read MoreThis short post will teach you what ransomware is and how to protect yourself. Indeed in recent times users, both at home and at work, are often rece
Read MorePenBox – A Penetration Testing Framework A Penetration Testing Framework , The Hacker’s Repo our hope is in the last version we will have every scrip
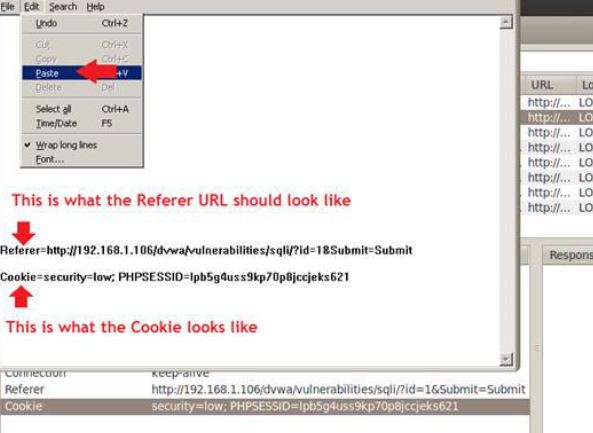
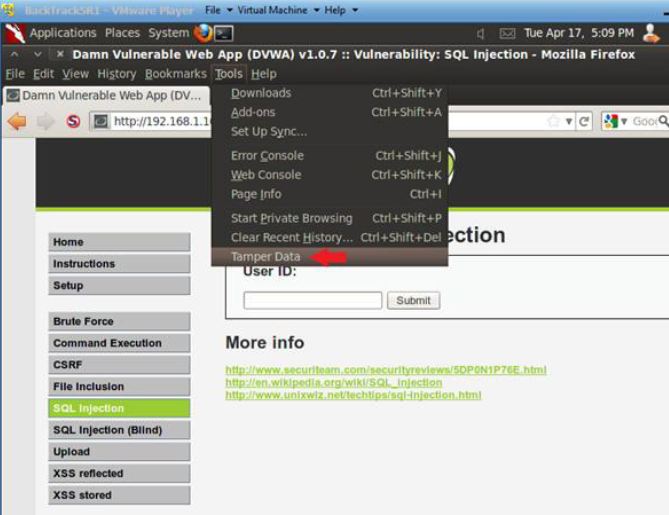
Read MoreWelcome Gurkhas, in Part 3 . . . Section 9: Obtain PHP Cookie 1. SQL Injection Menu o Instructions: 1. Select “SQL Injection” from the left naviga
Read MoreLet’s start part 2. Open Console Terminal and Retrieve IP Address open a console terminal Instructions: 1. Click on the console terminal
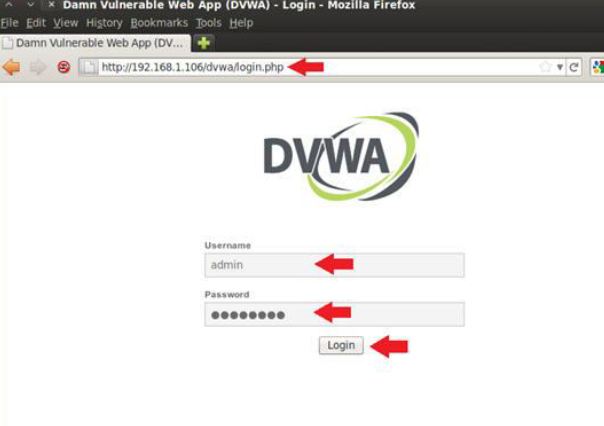
Read MoreIn this lab, We’ll begin the series of SQL Injection. This will be Part-Wise Article/Guide on SQL Injection. Let’s start from LAB setup : > Kali
Read MoreThe intricate details revolving around the security of personal and corporate accounts are often times not fully realized or understood and the measur
Read More