It seems like iPhone storage is always at a premium, especially if you have model with just 16GB... it's the rare user who doesn't know
Read More192.168.2.1 IP address – This is actually the default IP address of your home network for some of the popular broadband wireless routers such as SMC a
Read MoreOla the taxi aggregator based in India has been trying out everything to keep its competitor Uber far behind the company. The Indian Online taxi Aggre
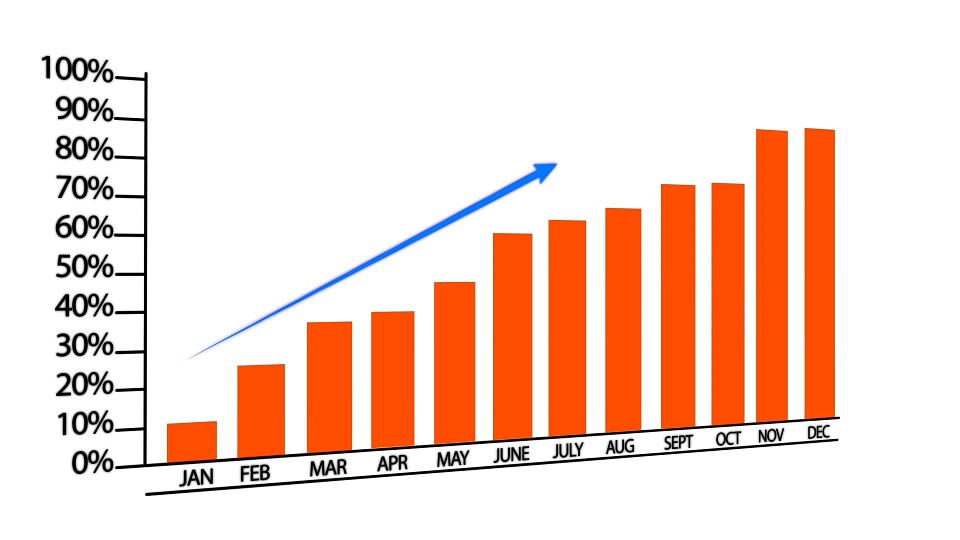
Read MoreBy now you must be aware that affiliate marketing is all about making angles. It is about creating a dance choreography that brings together merchants
Read MoreWe all know Kali Linux is Most Advanced Penetration Testing Distribution, Ever made. Most of the ethical hackers use Kali Linux for pen-testing.Usuall
Read MorePenBox – A Penetration Testing Framework A Penetration Testing Framework , The Hacker’s Repo our hope is in the last version we will have every scrip
Read MoreThe following is a brief reference to an effective - step by step - Pentesting process... Phase 1. Reconnaissance/Footprinting: This introduction
Read MoreHello, Readers , Today I'm gonna share how one can Learn Hacking and How to achieve your Hacking Goal. The word "HACK" (computer security) is one amon
Read MoreNowadays Whatsapp users are rapidly increasing like wildfire in a forest and many people want to have fun with their friends to fool them or to tease
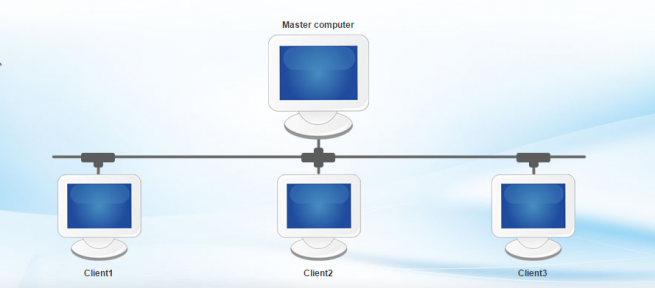
Read MorePXE booting is a wonderful and easy way to deploy and install operating systems on a lot of computers at once. PXE turns out to be very handy in educa
Read More